Who is Your Company's Riskiest User?
Download Sample M365 Risk AssessmentWouldn’t it be great if we could detect when our user accounts were being used in places it would have been impossible for us to travel to? How protected would you feel if you knew users exhibiting risky, anomalous behavior were automatically challenged for a second layer of authentication? Maybe we should run a system to alert administrators when these kinds of things were going on!
If you haven't guessed it so far, my cheesy delivery is failing. We can do all of that today.
Azure Active Directory Identity Protection is the very same security Microsoft uses to protect its own internal identities. It incorporates machine learning algorithms and heuristics to detect, assess and if configured, take action on suspicious behavior.
The automatic responses to risky situations means we can impose tougher security when it is called for, situationally. The user benefits because normal behavior is rewarded with a less authentication challenged experience. Automatic responses include multi-factor authentication enforcement or even a password reset. It can be tuned to be extremely sensitive to risk, or take action only when very obvious malicious activity is occurring.
We can report on the riskiest user accounts, review security posture recommendations and look at all of that on pretty dashboards.
I've included a few of the more interesting screenshots and the link to the Microsoft documentation on this technology.
Identity Protection capabilities
Detecting vulnerabilities and risky accounts:
- Providing custom recommendations to improve overall security posture by highlighting vulnerabilities
- Calculating sign-in risk levels
- Calculating user risk levels
Investigating risk events:
- Sending notifications for risk events
- Investigating risk events using relevant and contextual information
- Providing basic workflows to track investigations
- Providing easy access to remediation actions such as password reset
Risk-based conditional access policies:
- Policy to mitigate risky sign-ins by blocking sign-ins or requiring multi-factor authentication challenges.
- Policy to block or secure risky user accounts
- Policy to require users to register for multi-factor authentication
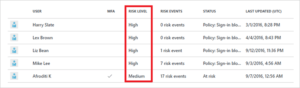
Identity Protection dashboard.
The dashboard gives you access to:
- Reports such as Users flagged for risk, Risk events and Vulnerabilities
- Settings such as the configuration of your Security Policies, Notifications and multi-factor authentication registration
Users flagged for risk dashboard
User risk levels
Review sign-ins from anonymous networks
It goes on, and alas I have brevity requirements to observe! If you want to know more about getting this enabled, the best practices surrounding these features or how you can utilize Azure Active Directory, a conversation would be a great starting point!
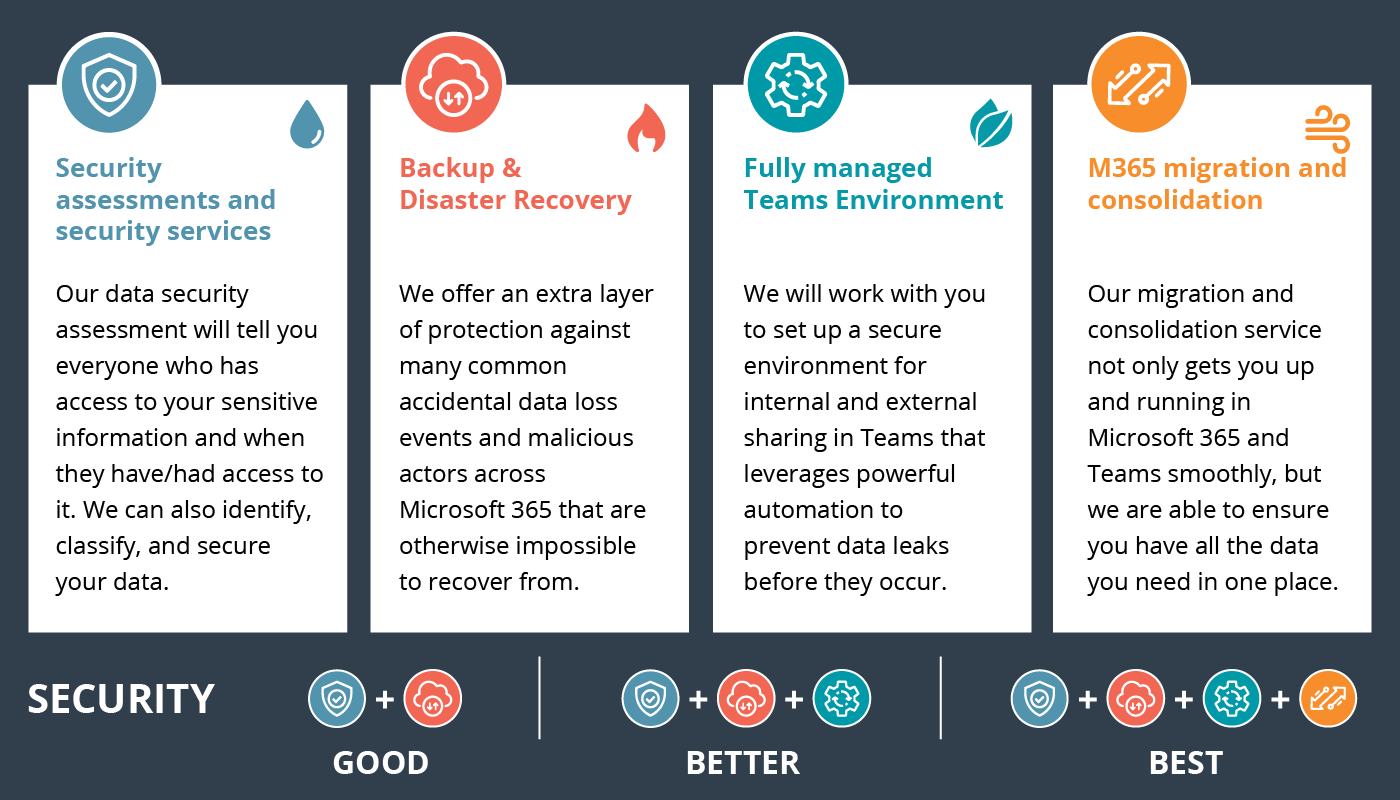
Solve Your IT Challenges
Increase your network's uptime and keep your connections secure with Akins IT
Attend An Event
Attend one of our events to learn something new from our partners and experts
Solve Your
IT Challenges
Increase your network's uptime and keep your connections secure with Akins IT.
arctic wolf labs
threat report 2024
This report offers expert insights into attack types, root causes, top vulnerabilities, TTPs, and more.
1301 Dove Street #130
Newport Beach, California 92660
Mailing Address:
3406 Via Lido, Suite 1A-22
Newport Beach, California 92663

All Rights Reserved | Akins IT | Privacy Policy | Terms of Service | Disclaimer
Website By: EnlightWorks